Cybersecurity software innovations pave the way for a fascinating exploration into the world of digital protection. From cutting-edge advancements to the evolving landscape of cybersecurity, this topic promises a deep dive into the realm of safeguarding our digital assets.
As we delve further into the intricacies of cybersecurity software innovations, we uncover the key trends, challenges, and advancements shaping the future of digital security.
Introduction to Cybersecurity Software Innovations
Cybersecurity software innovations refer to the continuous development and enhancement of tools and technologies designed to protect digital systems, networks, and data from cyber threats. These innovations play a crucial role in addressing the evolving landscape of cyber threats and ensuring the security and integrity of digital assets.Staying updated with the latest cybersecurity software advancements is essential in safeguarding against sophisticated cyber attacks.
As cyber threats continue to become more complex and sophisticated, outdated security measures may not provide sufficient protection. By embracing cybersecurity software innovations, organizations can strengthen their defense mechanisms and stay ahead of potential threats.The role of cybersecurity software in protecting digital assets cannot be overstated.
It serves as a frontline defense against a wide range of cyber threats, including malware, ransomware, phishing attacks, and data breaches. By implementing robust cybersecurity software solutions, organizations can proactively identify and mitigate security risks, prevent unauthorized access to sensitive information, and ensure the confidentiality, integrity, and availability of their data.
Trends in Cybersecurity Software Innovations
As technology advances, the landscape of cybersecurity software innovations continues to evolve rapidly. It is crucial to stay updated on the latest trends to ensure the protection of sensitive data and systems.
Modernization of Traditional Cybersecurity Approaches
Traditional cybersecurity approaches often relied on static rules and signatures to detect and prevent threats. However, modern software innovations are shifting towards more dynamic and adaptive solutions. By incorporating technologies such as artificial intelligence (AI) and machine learning, cybersecurity software can now analyze vast amounts of data in real-time to identify anomalies and potential threats proactively.
Impact of AI and Machine Learning
The integration of AI and machine learning in cybersecurity software development has revolutionized the way threats are detected and mitigated. These technologies enable systems to learn from past incidents and continuously improve their threat detection capabilities. By leveraging AI algorithms, cybersecurity software can detect patterns and anomalies that may go unnoticed by traditional security measures, enhancing overall protection.
Mobile App Development in Cybersecurity
Mobile app development plays a crucial role in enhancing cybersecurity measures in today’s digital landscape. With the increasing reliance on mobile devices for various tasks, securing these devices and the data they hold has become a top priority for individuals and organizations alike.
Examples of Mobile Apps Enhancing Cybersecurity Measures
- 1. Authy: This mobile app provides two-factor authentication for users, adding an extra layer of security beyond just passwords.
- 2. Lookout: Lookout is a mobile security app that protects against mobile threats, including malware, phishing, and data breaches.
- 3. LastPass: LastPass is a password manager app that securely stores all your passwords and sensitive information, ensuring they are encrypted and only accessible to you.
How Mobile App Development Contributes to a More Secure Digital Environment
Mobile app development contributes to a more secure digital environment by offering specialized tools and solutions to protect mobile devices from cyber threats. These apps help in securing data, preventing unauthorized access, and detecting and mitigating potential risks in real-time.
By leveraging mobile apps for cybersecurity, users can actively participate in safeguarding their digital identities and information, ultimately creating a more secure online space for everyone.
Software Development for Cybersecurity
In the realm of cybersecurity, software development plays a crucial role in creating robust solutions to protect sensitive data and systems from cyber threats. Developers follow a meticulous process to design, implement, and test cybersecurity software to ensure its effectiveness in safeguarding against malicious activities.
Challenges in Creating Secure Cybersecurity Software
Developers face numerous challenges when creating secure cybersecurity software, including:
- Complexity of Cyber Threats: With the ever-evolving nature of cyber threats, developers need to stay ahead of attackers by continuously updating and enhancing security measures.
- Vulnerabilities in Code: Writing secure code is essential to prevent vulnerabilities that can be exploited by hackers to compromise systems.
- Compliance Requirements: Meeting stringent regulatory compliance standards adds an additional layer of complexity to the development process.
- Integration Issues: Ensuring seamless integration with existing systems and applications without compromising security is a significant challenge.
Agile Methodologies in Cybersecurity Software Development
Agile software development methodologies are increasingly being adopted in the cybersecurity industry to enhance flexibility and responsiveness in addressing security needs. Some key methodologies include:
- Scrum: A framework that emphasizes collaboration, accountability, and iterative progress to deliver high-quality software.
- Kanban: Focuses on continuous delivery and workflow efficiency by visualizing work and limiting work in progress.
- DevOps: Combines development and operations teams to streamline the software delivery process and improve collaboration.
Mobile Technology and Cybersecurity
Mobile technology has become an integral part of our daily lives, with smartphones and tablets being used for communication, online transactions, social media, and much more. However, these devices are also vulnerable to cyber threats, making cybersecurity software essential in protecting them.
Mobile Vulnerabilities and Cybersecurity
- Mobile devices are more prone to malware attacks due to the vast amount of personal data stored on them.
- Public Wi-Fi networks pose a significant risk as they can be easily compromised by hackers looking to intercept sensitive information.
- Phishing scams through text messages or malicious apps can trick users into providing login credentials or financial details.
Role of Cybersecurity Software in Mobile Protection
- Cybersecurity software for mobile devices provides features like antivirus protection, data encryption, and secure VPN connections.
- These tools help in detecting and removing malware, securing sensitive data, and encrypting communications to prevent unauthorized access.
- Regular software updates are crucial to patch vulnerabilities and ensure the latest security protocols are in place.
Importance of Integrating Cybersecurity Features into Mobile Technology
- With the increasing use of mobile devices for work and personal tasks, the risk of cyber attacks targeting these devices has also grown.
- Integrating cybersecurity features directly into mobile technology ensures a proactive approach to security, safeguarding user data and privacy.
- By prioritizing cybersecurity in mobile development, users can have peace of mind knowing that their devices are protected from potential threats.
Technology & Software Innovations in Cybersecurity

Technology and software innovations in the cybersecurity sector have been rapidly evolving to keep up with the ever-changing landscape of cyber threats. These advancements have revolutionized the way organizations protect their sensitive data and systems from malicious attacks. Let’s explore some recent developments in cybersecurity technology and software.
Artificial Intelligence and Machine Learning
Artificial Intelligence (AI) and Machine Learning (ML) have become integral parts of cybersecurity tools and software. These technologies enable systems to detect and respond to threats in real-time, helping organizations stay ahead of cybercriminals. AI-powered solutions can analyze vast amounts of data to identify patterns and anomalies that may indicate a potential security breach.
Zero Trust Architecture
Zero Trust Architecture is a security model that assumes no user or device within a network can be trusted by default. This approach requires strict identity verification and access controls for every user and device trying to connect to the network.
By implementing Zero Trust Architecture, organizations can mitigate the risk of insider threats and unauthorized access to sensitive information.
Quantum Cryptography
Quantum Cryptography is a cutting-edge technology that leverages the principles of quantum mechanics to secure communications and data transmissions. Unlike traditional encryption methods, which can be vulnerable to attacks from quantum computers, Quantum Cryptography uses quantum key distribution to ensure data security.
This innovative approach is poised to revolutionize the field of cybersecurity in the coming years.
Blockchain Technology
Blockchain technology, known primarily for its role in cryptocurrencies, is also being increasingly adopted in cybersecurity applications. By using decentralized and tamper-proof ledgers, blockchain can enhance data integrity, authentication, and secure transactions. This technology is particularly valuable in ensuring the integrity of critical information and preventing data tampering.
Web Development for Cybersecurity
Web development plays a crucial role in cybersecurity by ensuring that websites and web applications are built with security in mind. The relationship between web development and cybersecurity is essential for protecting users’ data and preventing cyber attacks.
Best Practices for Integrating Cybersecurity Features into Web Development
- Implementing secure coding practices: Web developers should follow secure coding guidelines to prevent vulnerabilities such as SQL injection, Cross-Site Scripting (XSS), and Cross-Site Request Forgery (CSRF).
- Regular security testing: Conducting regular security testing, such as penetration testing and vulnerability scanning, can help identify and address security issues in web applications.
- Using HTTPS encryption: Encrypting data transmitted between the web server and the user’s browser using HTTPS helps protect sensitive information from being intercepted by malicious actors.
- Implementing strong authentication mechanisms: Utilizing multi-factor authentication and strong password policies can enhance the security of web applications and prevent unauthorized access.
Role of Web Developers in Ensuring Secure Online Experiences
- Updating software and libraries: Web developers should regularly update software and libraries used in web development to patch known security vulnerabilities.
- Securing databases: Implementing proper database security measures, such as encryption and access controls, can prevent data breaches and unauthorized access to sensitive information.
- Monitoring for security incidents: Web developers play a crucial role in monitoring web applications for security incidents and responding promptly to mitigate risks.
Networking and Cybersecurity Software
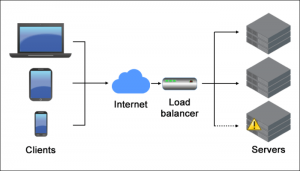
In today’s digital landscape, networking plays a crucial role in the realm of cybersecurity software. As businesses and individuals connect through various networks, the need for robust cybersecurity measures to protect sensitive data and systems becomes increasingly important. Cybersecurity software innovations have been instrumental in enhancing network security and safeguarding against evolving threats.
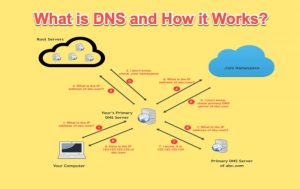
The Importance of Networking in Cybersecurity Software
Networking serves as the foundation for communication and data exchange in the digital world. In the context of cybersecurity software, networks are the pathways through which information travels, making them vulnerable to cyber attacks. Securing these networks is essential to prevent unauthorized access, data breaches, and other malicious activities.
Innovative cybersecurity solutions are designed to strengthen network defenses and mitigate potential risks.
- Implementing firewalls and intrusion detection systems to monitor and filter incoming and outgoing network traffic.
- Utilizing virtual private networks (VPNs) to create secure connections over public networks and encrypt data transmissions.
- Deploying network segmentation to separate critical assets from less secure areas and limit the impact of potential breaches.
- Conducting regular network assessments and penetration testing to identify vulnerabilities and address security gaps proactively.
Effective network security is essential in safeguarding sensitive information and maintaining the integrity of digital assets.
Challenges of Securing Networks in the Digital Age
Securing networks in the digital age presents numerous challenges due to the increasing complexity of cyber threats and the expanding attack surface. With the rise of remote work, cloud computing, and IoT devices, networks are more susceptible to cyber attacks than ever before.
Innovative cybersecurity solutions are needed to address these challenges and protect network infrastructures effectively.
- Managing the security of interconnected devices and systems within a network to prevent potential vulnerabilities.
- Detecting and responding to advanced persistent threats (APTs) and sophisticated cyber attacks that target network infrastructure.
- Ensuring compliance with data protection regulations and industry standards to avoid costly fines and reputational damage.
- Balancing network performance and security requirements to maintain operational efficiency while minimizing risks.
As cyber threats continue to evolve, organizations must stay ahead of the curve by adopting innovative cybersecurity solutions that address the unique challenges of securing networks in the digital age.
Gaming Hardware and Cybersecurity
When it comes to gaming hardware, cybersecurity plays a crucial role in ensuring the protection of user data and systems. The intersection of gaming hardware and cybersecurity brings about unique challenges and vulnerabilities that need to be addressed.
Vulnerabilities in Gaming Hardware
One of the main vulnerabilities associated with gaming hardware is the potential for cyberattacks to compromise user data and system integrity. Hackers may exploit weaknesses in gaming devices to gain unauthorized access, steal personal information, or disrupt gameplay.
- Gaming hardware often contains sensitive data such as payment information, personal details, and login credentials, making them attractive targets for cybercriminals.
- Outdated firmware or lack of security features in gaming devices can leave them vulnerable to malware, ransomware, and other cyber threats.
- Online gaming platforms and multiplayer games create additional risks, as cybercriminals may use social engineering tactics to trick users into downloading malicious software.
Cybersecurity Software Innovations for Gaming Systems
Cybersecurity software innovations are continuously evolving to protect gaming systems and user data from cyber threats. Developers are implementing advanced security measures to safeguard gaming hardware and ensure a safe gaming experience for users.
- Anti-malware programs specifically designed for gaming devices can detect and remove malicious software, protecting systems from cyberattacks.
- Encryption technologies help secure communication between gaming hardware and servers, preventing unauthorized access to sensitive data.
- Multi-factor authentication and biometric recognition add an extra layer of security to gaming systems, reducing the risk of unauthorized account access.
Smart Technology and Cybersecurity
Smart technology refers to devices and systems that are connected to the internet and can communicate with each other to make intelligent decisions. This includes smart home devices, wearable technology, and IoT devices. While smart technology offers convenience and efficiency, it also poses significant cybersecurity risks.
Cybersecurity Risks of Smart Technology
- Increased Attack Surface: Smart devices create new entry points for cybercriminals to exploit, leading to more vulnerabilities in the system.
- Privacy Concerns: Smart devices collect and transmit personal data, making them attractive targets for data breaches.
- Insecure Communication: Inadequately secured communication channels between smart devices can be intercepted by hackers, compromising sensitive information.
- Weak Authentication: Many smart devices come with default passwords or lack strong authentication mechanisms, making them easy targets for brute force attacks.
Cybersecurity Innovations for Smart Technology
- Secure Firmware Updates: Implementing secure over-the-air firmware updates can help patch vulnerabilities and enhance the security of smart devices.
- IoT Security Standards: Developing industry-wide security standards for IoT devices can ensure that manufacturers follow best practices for cybersecurity.
- Behavioral Analytics: Using AI-powered behavioral analytics can help detect anomalies in smart device behavior and identify potential security threats.
- Network Segmentation: Segregating smart devices on separate networks can limit the impact of a security breach and prevent lateral movement by hackers.
Final Conclusion

In conclusion, cybersecurity software innovations play a crucial role in fortifying our digital defenses and adapting to the ever-changing landscape of cyber threats. By staying informed and embracing new technologies, we can build a more resilient and secure online environment for all.
Query Resolution
How do cybersecurity software innovations impact data protection?
Cybersecurity software innovations enhance data protection by introducing advanced encryption methods and real-time threat detection.
What role does AI play in modern cybersecurity software?
AI is instrumental in cybersecurity software by automating threat analysis, identifying patterns, and improving overall security measures.
Are there any notable cybersecurity software trends to watch for in the coming years?
Some emerging trends include the rise of zero-trust security models, the integration of blockchain technology, and the focus on cloud security solutions.