Network load balancing techniques sets the stage for this enthralling narrative, offering readers a glimpse into a story that is rich in detail and brimming with originality from the outset. In today’s interconnected world, the efficient distribution of network traffic is crucial for optimal performance and reliability.
This guide will delve into various strategies and algorithms that play a key role in achieving seamless network load balancing.
Network Load Balancing Techniques
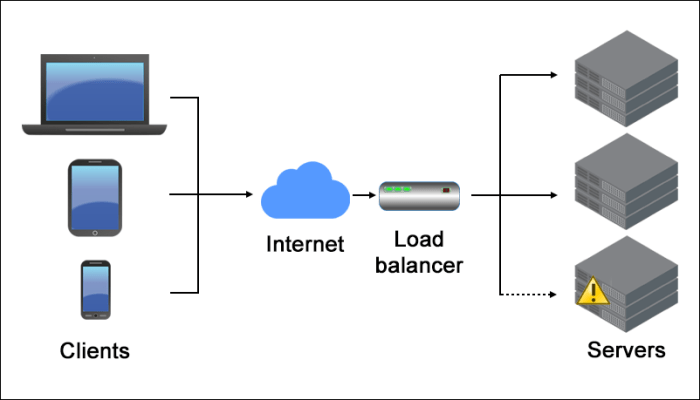
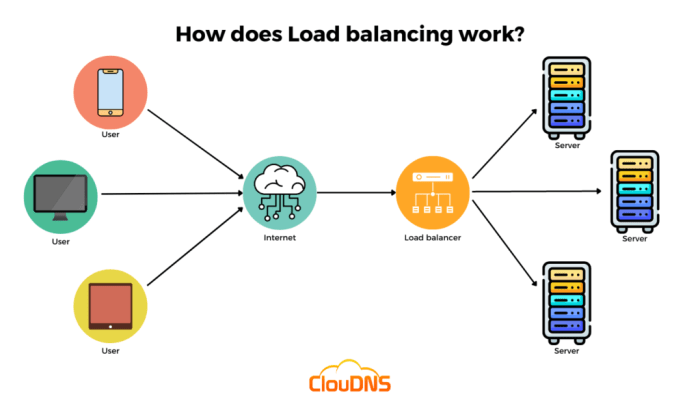
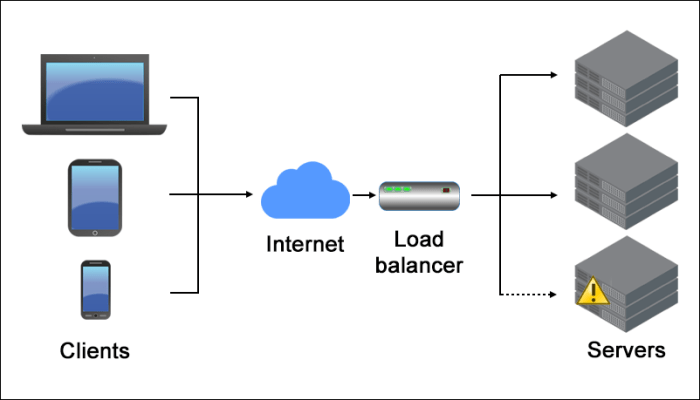
Network load balancing is a method used to distribute network traffic across multiple servers or network resources to prevent any single server from getting overwhelmed and ensure optimal utilization of resources.
Examples of Network Load Balancing Algorithms
- Round Robin: This algorithm distributes traffic evenly across servers in a circular manner, sending each new request to the next server in line.
- Least Connections: This algorithm directs traffic to the server with the fewest active connections at the time, ensuring a more balanced distribution of load.
- Weighted Round Robin: In this algorithm, servers are assigned different weights based on their processing power or capacity, allowing heavier servers to receive more traffic.
Importance of Network Load Balancing, Network load balancing techniques
Network load balancing plays a crucial role in improving network performance by ensuring high availability, scalability, and reliability. It helps prevent server overload, reduces downtime, and enhances overall user experience by efficiently distributing network traffic.
Network Management
Network management plays a crucial role in maintaining network efficiency by ensuring that all network components are functioning optimally and effectively.
Network Management Tools and Functionalities
There are various network management tools available, each with its own set of functionalities to help monitor, control, and optimize network performance.
- Network Monitoring Tools: These tools help in real-time monitoring of network performance, bandwidth usage, and device status.
- Configuration Management Tools: These tools assist in configuring and managing network devices, ensuring consistency and compliance with standards.
- Performance Management Tools: These tools focus on analyzing network performance metrics, identifying bottlenecks, and optimizing network resources.
- Security Management Tools: These tools help in detecting and preventing security breaches, ensuring the network’s safety and integrity.
Best Practices for Effective Network Management Strategies
Implementing the following best practices can help in enhancing network management efficiency:
- Regular Monitoring and Analysis: Continuously monitor network performance metrics and analyze data to identify issues proactively.
- Automation: Utilize automation tools to streamline repetitive tasks, reduce manual errors, and improve operational efficiency.
- Regular Updates and Patch Management: Keep network devices up to date with the latest software updates and security patches to prevent vulnerabilities.
- Network Segmentation: Segment the network to isolate critical assets and improve security by controlling access to sensitive data.
- Disaster Recovery Planning: Develop a comprehensive disaster recovery plan to minimize network downtime and ensure quick recovery in case of failures.
Network Forensics: Network Load Balancing Techniques
Network forensics is a crucial aspect of cybersecurity that involves the monitoring and analysis of network traffic to gather evidence for investigating security incidents or breaches. By examining network data, such as logs and packet captures, network forensics helps in identifying the root cause of an attack, understanding the extent of the damage, and implementing measures to prevent future incidents.
Process of Conducting Network Forensics Investigations
- Identification of the Incident: The first step involves detecting unusual network behavior or security alerts that indicate a potential breach.
- Data Collection: Relevant network data, including logs, packet captures, and configuration files, are collected for analysis.
- Data Analysis: Network traffic is examined to uncover the timeline of events, identify the attack vectors, and determine the impact on the network.
- Forensic Reporting: Findings from the analysis are documented in a detailed report for further investigation or legal proceedings.
Challenges in Network Forensics and Solutions
- Encryption: Encrypted traffic poses a challenge as it limits visibility into the data exchanged. Employing decryption tools or monitoring encrypted traffic can help overcome this obstacle.
- Data Volume: The sheer volume of network data can make it challenging to sift through relevant information. Utilizing automated tools for data analysis and filtering can streamline the process.
- Data Integrity: Ensuring the integrity of collected evidence is crucial for its admissibility in legal proceedings. Implementing secure storage mechanisms and maintaining a chain of custody can address this challenge.
- Timeliness: Conducting network forensics in a timely manner is essential to prevent further damage and preserve evidence. Having predefined response procedures and dedicated resources can help in expediting investigations.
Home Networks
Home networks are essential for connecting multiple devices within a household to the internet, allowing for seamless communication, entertainment, and productivity. However, these networks can also be vulnerable to cyber threats if not properly secured. It is important to understand common network setups in home environments and implement best practices to optimize connectivity and protect against potential risks.
Common Network Setups in Home Environments
Home networks typically consist of a modem connected to a router, which distributes the internet connection to various devices through wired or wireless connections. It is common to have smartphones, laptops, smart TVs, gaming consoles, and other smart devices connected to the network simultaneously.
- Ensure your router firmware is up to date to address any security vulnerabilities.
- Change the default administrator password on your router to prevent unauthorized access.
- Enable encryption (WPA2 or WPA3) on your Wi-Fi network to secure communication between devices.
- Use strong, unique passwords for your Wi-Fi network and all connected devices to prevent unauthorized access.
Securing Home Networks from Cyber Threats
Securing your home network is crucial to protect sensitive information and prevent unauthorized access to your devices. Implementing the following tips can help enhance the security of your network:
- Enable firewall protection on your router to filter incoming and outgoing traffic.
- Use a virtual private network (VPN) to encrypt your internet connection and safeguard your data when accessing the internet.
- Regularly update the software on all connected devices to patch security vulnerabilities.
- Disable remote management features on your router to prevent external tampering.
Optimizing Home Networks for Better Connectivity
Optimizing your home network can improve the speed and reliability of your internet connection, ensuring a seamless online experience for all devices. Consider the following strategies to optimize your home network:
- Position your router in a central location to provide equal coverage to all areas of your home.
- Reduce interference by placing your router away from electronic devices that emit signals, such as microwaves and cordless phones.
- Upgrade your router to a newer model that supports the latest Wi-Fi standards for faster speeds and improved performance.
- Use wired connections for devices that require high bandwidth, such as gaming consoles or smart TVs, to reduce latency and ensure stable connectivity.
Closing Summary
As we conclude this exploration of network load balancing techniques, it becomes evident that mastering these strategies is essential for enhancing network performance and ensuring a seamless user experience. By implementing the right load balancing algorithms and practices, organizations can effectively distribute traffic, prevent bottlenecks, and optimize their network infrastructure.
Top FAQs
What are the key benefits of network load balancing?
Network load balancing helps in optimizing resource utilization, improving response times, enhancing reliability, and ensuring high availability of network services.
How do network load balancing algorithms work?
These algorithms distribute incoming network traffic across multiple servers or resources to prevent overloading and ensure efficient utilization of resources.
What are some common challenges in implementing network load balancing?
Some challenges include configuration complexity, ensuring compatibility with different network architectures, and maintaining consistent performance across varying workloads.