Exploring how small businesses can enhance their cybersecurity measures opens up a world of possibilities. From identifying common threats to discussing effective risk assessment strategies, this topic delves into the intricate web of cybersecurity tailored for small business needs.
As we navigate through the various aspects of cybersecurity implementation, a comprehensive guide awaits to equip small businesses with the necessary tools and knowledge to safeguard their digital assets.
Overview of Cybersecurity Measures for Small Businesses
Cybersecurity is crucial for small businesses to protect their sensitive data, financial information, and reputation from cyber threats. Implementing robust cybersecurity measures is essential to safeguard business operations and maintain trust with customers.
The Importance of Cybersecurity for Small Businesses
Small businesses often underestimate the importance of cybersecurity, assuming they are not a target for cyber attacks. However, cybercriminals view small businesses as easy targets due to their limited resources and minimal security measures in place. Investing in cybersecurity can prevent costly data breaches, financial losses, and damage to the business’s reputation.
Common Cybersecurity Threats Faced by Small Businesses
- Phishing attacks: Cybercriminals use deceptive emails or messages to trick employees into revealing sensitive information or downloading malware.
- Ransomware: Malicious software that encrypts data and demands payment for decryption, posing a significant threat to small businesses.
- Weak passwords: Using easily guessable passwords or not implementing multi-factor authentication leaves small businesses vulnerable to unauthorized access.
- Unsecure Wi-Fi networks: Without proper encryption and security protocols, Wi-Fi networks can be exploited by cybercriminals to intercept sensitive data.
Potential Consequences of a Cyber Attack on a Small Business
- Data breaches: Loss of sensitive customer information can result in financial penalties, legal consequences, and damage to the business’s reputation.
- Financial losses: Cyber attacks can disrupt business operations, leading to financial losses due to ransom payments, downtime, and recovery costs.
- Reputation damage: A cyber attack can erode customer trust and loyalty, impacting the long-term success and viability of the small business.
Risk Assessment and Planning
When it comes to cybersecurity for small businesses, conducting a thorough risk assessment and creating a tailored cybersecurity plan are crucial steps to protect sensitive data and systems.
Conducting a Cybersecurity Risk Assessment
A cybersecurity risk assessment involves identifying, analyzing, and evaluating potential risks that could compromise the security of your small business. Here are the steps involved:
- Evaluate current security measures in place.
- Identify potential vulnerabilities in systems and processes.
- Assess the likelihood and impact of various cyber threats.
- Determine the assets that need to be protected.
- Document findings and prioritize risks based on severity.
Creating a Cybersecurity Plan
Once the risks have been assessed, it’s important to develop a cybersecurity plan that addresses the specific needs of your small business. Here are key elements to consider:
- Establish security policies and procedures for employees.
- Implement strong access controls and user authentication.
- Regularly update software and systems to patch vulnerabilities.
- Encrypt sensitive data both in transit and at rest.
- Backup critical data regularly and test restoration processes.
Employee Training and Awareness
Educating employees about cybersecurity best practices is crucial for small businesses to protect their sensitive data and prevent cyber attacks. By raising awareness and providing proper training, employees can become the first line of defense against potential security breaches.
Examples of Cybersecurity Training Programs
- Online Security Training Courses: Platforms like Cybrary and SANS offer affordable online courses tailored for small businesses.
- Simulated Phishing Exercises: Services like KnowBe4 allow businesses to simulate phishing attacks to educate employees on how to identify and respond to such threats.
- Regular Workshops and Seminars: Hosting regular cybersecurity workshops and seminars can help reinforce best practices and keep employees informed about the latest threats.
Raising Cybersecurity Awareness
It is essential to continuously raise cybersecurity awareness among employees to ensure that they remain vigilant and proactive in protecting company data. Here are some effective strategies to achieve this:
- Regular Communication: Provide regular updates on cybersecurity threats and best practices through emails, newsletters, or team meetings.
- Security Policies and Procedures: Clearly communicate security policies and procedures to all employees and ensure they understand their roles and responsibilities in maintaining cybersecurity.
- Training and Testing: Conduct regular training sessions and testing to evaluate employees’ knowledge and awareness of cybersecurity practices.
- Reward System: Implement a reward system to incentivize employees who demonstrate good cybersecurity practices and report potential security risks.
Data Protection and Encryption
Data protection is crucial for small businesses to safeguard sensitive information from unauthorized access or breaches. Implementing encryption methods can help in securing data and preventing potential cyber threats.
Encryption Methods
- End-to-End Encryption: This method ensures that data is encrypted from the sender to the receiver, making it unreadable to anyone in between.
- File-Level Encryption: Encrypting individual files or folders to protect specific data from being compromised.
- Full Disk Encryption: Encrypting the entire hard drive to secure all data stored on the device.
Tools and Software for Encryption
- BitLocker: A built-in encryption tool in Windows operating systems to encrypt drives.
- VeraCrypt: An open-source encryption tool for creating encrypted containers or full disk encryption.
- SSL/TLS Certificates: Used to encrypt data transmitted over the internet, ensuring secure communication.
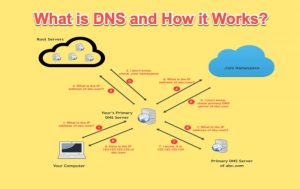
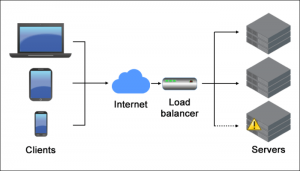
Secure Network Infrastructure
In today’s digital age, securing your small business’s network infrastructure is crucial to protecting sensitive data and preventing cyber attacks. By implementing the right network security measures, you can safeguard your business from potential threats and ensure smooth operations.
Firewalls and VPNs
Firewalls act as a barrier between your internal network and external threats, filtering out malicious traffic and unauthorized access. VPNs (Virtual Private Networks) encrypt data transmitted over the network, making it more difficult for hackers to intercept sensitive information.
- Firewalls: Firewalls can be hardware or software-based and help prevent unauthorized access to your network by monitoring incoming and outgoing traffic.
- VPNs: VPNs create a secure connection over the internet, allowing remote employees to access company resources securely and encrypting data to protect it from cyber threats.
Regular Network Monitoring and Updates
Regular monitoring of your network allows you to detect unusual activities or security breaches promptly. Updates to network security software, firmware, and patches help address vulnerabilities and strengthen your defenses against evolving cyber threats.
Regular network monitoring and updates are essential in maintaining a secure network infrastructure and protecting your small business from cyber attacks.
Incident Response and Recovery
Developing an incident response plan is crucial for small businesses to effectively address cybersecurity incidents. This plan Artikels the steps to take in case of a data breach or cyber attack, helping minimize damage and facilitate a swift recovery.
Importance of Regular Backups and Data Recovery Strategies
Regular backups of critical data are essential to ensure that information can be restored in case of a cybersecurity incident. Implementing data recovery strategies, such as cloud storage or offsite backups, can help small businesses recover quickly and minimize downtime in the event of a breach.
- Regularly back up all important data and systems to secure locations.
- Implement automated backup processes to ensure consistency and reliability.
- Test data recovery procedures regularly to confirm their effectiveness.
Testing and Improving Incident Response Procedures
Regular testing of incident response procedures is vital to identify weaknesses and areas for improvement. By conducting simulated cyber attack scenarios, small businesses can evaluate the effectiveness of their response plan and make necessary adjustments to enhance their cybersecurity posture.
Regularly review and update the incident response plan based on lessons learned from testing and real-life incidents.
- Conduct tabletop exercises to simulate cyber attack scenarios and evaluate response capabilities.
- Involve key stakeholders in testing and refining incident response procedures.
- Document lessons learned from testing and incorporate feedback to enhance response effectiveness.
Mobile App Development
In today’s digital age, mobile applications play a crucial role in the business world. As more businesses rely on mobile apps to connect with customers and streamline operations, the importance of cybersecurity in mobile app development cannot be overstated. Ensuring the security of mobile apps is essential to protect sensitive data, maintain user trust, and safeguard against cyber threats.
Common Vulnerabilities in Mobile Apps and How to Address Them
When developing a mobile app, it is important to be aware of common vulnerabilities that can compromise its security. Some of these vulnerabilities include insecure data storage, insufficient encryption, weak authentication mechanisms, and inadequate input validation. To address these vulnerabilities and enhance cybersecurity in mobile app development, best practices should be followed.
- Implement Secure Data Storage: Utilize encryption techniques to secure sensitive data stored on the device, such as user credentials, payment information, and personal details.
- Use Strong Encryption: Ensure that all data transmission between the app and servers is encrypted using secure protocols like SSL/TLS to prevent eavesdropping and data breaches.
- Enhance Authentication: Implement multi-factor authentication, biometric authentication, or other strong authentication methods to verify user identities and prevent unauthorized access.
- Validate User Inputs: Validate and sanitize user inputs to prevent injection attacks, such as SQL injection or cross-site scripting, which can lead to data manipulation or theft.
Best Practices for Integrating Cybersecurity Measures into Mobile App Development
Integrating cybersecurity measures into mobile app development should be a priority from the initial stages of planning and design. By following best practices, developers can create secure and resilient mobile apps that protect both the business and its users from cyber threats.
- Conduct Security Testing: Perform regular security testing, including penetration testing and code reviews, to identify and remediate vulnerabilities in the app.
- Stay Updated: Keep the app updated with the latest security patches and software updates to address known vulnerabilities and protect against emerging threats.
- Follow Secure Coding Practices: Adhere to secure coding practices, such as input validation, least privilege, and secure configurations, to minimize the risk of security breaches.
- Educate Developers: Provide cybersecurity training and awareness programs for developers to enhance their understanding of secure coding principles and practices.
Software Development
When it comes to software development for small businesses, cybersecurity plays a crucial role in ensuring the protection of sensitive data and systems. Implementing secure coding practices is essential to enhance cybersecurity measures in software development.
Role of Cybersecurity in Software Development
Secure coding practices involve writing code in a way that prioritizes security from the initial stages of development. This includes identifying and mitigating potential vulnerabilities, implementing encryption techniques, and following coding best practices to prevent cyber threats.
- Utilizing input validation to prevent injection attacks
- Implementing proper authentication and authorization mechanisms
- Regularly updating software components to address security vulnerabilities
Tools and Frameworks for Building Secure Software
There are various tools and frameworks available that can assist small businesses in developing secure software:
Static analysis tools such as Veracode and Checkmarx can help identify security flaws in the code during the development process.
- OWASP (Open Web Application Security Project) provides a set of guidelines and resources for secure software development.
- Using secure development frameworks like Spring Security for Java applications can enhance security measures.
- Implementing secure coding standards such as CERT Secure Coding Standards can ensure that best practices are followed.
Cybersecurity and Mobile Technology
Mobile technology has become an integral part of small businesses, providing flexibility and convenience. However, with this increased reliance on mobile devices comes the need to address cybersecurity concerns to protect sensitive data. In this section, we will explore the intersection of cybersecurity and mobile technology for small businesses, discussing challenges, solutions, and trends impacting cybersecurity in this context.
Mobile Security Challenges and Solutions
Mobile devices present unique security challenges for small businesses, including the risk of data breaches, unauthorized access, and malware attacks. To address these challenges, businesses can implement the following solutions:
- Enforce strong authentication methods such as biometric recognition or multi-factor authentication for accessing mobile devices.
- Regularly update mobile operating systems and applications to patch security vulnerabilities.
- Implement mobile device management (MDM) solutions to monitor and control device usage within the organization.
- Train employees on mobile security best practices, such as avoiding public Wi-Fi networks and using secure communication channels.
Mobile Technology Trends Impacting Cybersecurity
As mobile technology continues to evolve, several trends are influencing cybersecurity for small businesses:
- Internet of Things (IoT) devices connected to mobile networks introduce new entry points for cyber threats.
- 5G technology offers faster data speeds but also presents security challenges due to increased network traffic.
- Mobile payment systems and digital wallets require robust security measures to protect financial transactions.
- Bring Your Own Device (BYOD) policies allow employees to use personal devices for work, increasing the risk of data leakage and unauthorized access.
Technology & Software for Small Businesses

Small businesses can greatly benefit from utilizing essential technologies and software tools to enhance their cybersecurity measures. By investing in cybersecurity software solutions tailored to their specific needs, small businesses can better protect their data and systems from cyber threats.
Leveraging technology effectively can strengthen their overall cybersecurity posture and ensure business continuity.
Essential Technologies and Software Tools
- Firewalls: Implementing firewalls can help small businesses control incoming and outgoing network traffic, serving as a barrier against unauthorized access.
- Antivirus Software: Installing antivirus software can detect and remove malware, viruses, and other malicious threats from devices and networks.
- Multi-Factor Authentication (MFA): Enabling MFA adds an extra layer of security by requiring users to provide multiple forms of verification to access accounts or systems.
- Encryption Tools: Utilizing encryption tools can protect sensitive data by converting it into a coded format that can only be accessed with the right decryption key.
Cybersecurity Software Solutions for Small Businesses
- Endpoint Protection Platforms: These solutions offer comprehensive security for devices like laptops, smartphones, and tablets, protecting them from cyber threats.
- Security Information and Event Management (SIEM) Software: SIEM tools help small businesses monitor and analyze security events in real-time to detect and respond to potential threats.
- Password Management Tools: Password managers can securely store and manage login credentials, ensuring strong and unique passwords for different accounts.
Web Development and Cybersecurity
In today’s digital age, cybersecurity plays a crucial role in web development for small businesses. It is essential to prioritize security measures to protect sensitive data and information from cyber threats.
Common Web Security Threats and Mitigation
When it comes to web development, small businesses face various security threats that can compromise the integrity of their websites. Some common threats include:
- Malware Infections: Malicious software can infect websites and steal sensitive information. Implementing regular malware scans and security updates can help mitigate this threat.
- Phishing Attacks: Cybercriminals may use phishing emails to trick users into providing confidential information. Educating employees and implementing email filters can help prevent phishing attacks.
- SQL Injection: Attackers exploit vulnerabilities in web applications to gain unauthorized access to databases. Validating user input and using parameterized queries can help prevent SQL injection attacks.
Tips for Integrating Cybersecurity Best Practices
To enhance cybersecurity in web development for small businesses, consider the following tips:
- Use Secure Coding Practices: Implement secure coding standards to prevent vulnerabilities in web applications.
- Secure Data Transmission: Utilize encryption protocols like SSL/TLS to secure data transmitted between the web server and client.
- Regular Security Audits: Conduct routine security audits to identify and address potential vulnerabilities in web applications.
- Backup and Recovery Plan: Develop a backup and recovery plan to ensure the quick restoration of data in case of a cyber incident.
Networking for Small Businesses
Secure networking is crucial for small businesses to protect their sensitive information and prevent cyber attacks. By implementing proper networking protocols and practices, small businesses can significantly enhance their cybersecurity posture.
Importance of Secure Networking
Secure networking ensures that data transmitted between devices within the network is encrypted and protected from unauthorized access. It helps prevent data breaches and unauthorized access to sensitive information.
- Implementing firewalls to monitor and control incoming and outgoing network traffic.
- Using Virtual Private Networks (VPNs) to create secure connections for remote employees.
- Regularly updating network equipment and software to patch vulnerabilities.
Network Security Solutions
There are several network security solutions suitable for small business environments to enhance cybersecurity:
| Intrusion Detection Systems (IDS) | Monitor network traffic for suspicious activity and alert administrators to potential threats. |
| Unified Threat Management (UTM) | Integrate multiple security features like firewall, antivirus, and intrusion prevention to protect the network. |
| Network Segmentation | Divide the network into segments to limit the spread of malware and unauthorized access. |
Gaming Hardware and Cybersecurity Measures
When it comes to small businesses, the use of gaming hardware can introduce unique cybersecurity challenges. It’s essential to understand the potential risks associated with gaming hardware in a business setting and how to secure it effectively to maintain cybersecurity.
Cybersecurity Risks with Gaming Hardware
Using gaming hardware in a business environment can pose various cybersecurity risks, including:
- Increased exposure to malware and viruses due to frequent online gaming activities
- Potential vulnerabilities in gaming peripherals that could be exploited for unauthorized access
- Risk of data breaches if gaming hardware is not properly secured and monitored
Securing Gaming Hardware for Small Businesses
Here are some tips to help small businesses secure gaming hardware effectively:
- Regularly update gaming hardware drivers and firmware to patch security vulnerabilities
- Implement strong password policies for gaming accounts and devices
- Use encryption tools to protect sensitive data stored or processed on gaming hardware
- Restrict access to gaming hardware only to authorized personnel
- Monitor gaming hardware for any unusual activity that could indicate a security breach
Smart Technology and Security
Smart technology has become increasingly popular in small businesses due to its efficiency and convenience. However, with this adoption comes security implications that need to be addressed to protect sensitive data and systems.
Security Challenges of Smart Technology Integration
- Increased attack surface: Smart devices connected to the network provide additional entry points for cybercriminals to exploit.
- Weak authentication methods: Many smart devices come with default passwords or lack robust authentication measures, making them vulnerable to unauthorized access.
- Data privacy concerns: Smart devices collect and transmit data, raising privacy issues if not properly secured.
- Lack of security updates: Some smart devices may not receive regular security updates, leaving them exposed to known vulnerabilities.
Best Practices for Securing Smart Devices
- Change default passwords: Ensure all smart devices have strong, unique passwords to prevent unauthorized access.
- Enable encryption: Encrypt data transmitted between smart devices and networks to protect it from interception.
- Update firmware regularly: Keep smart devices up to date with the latest security patches to mitigate known vulnerabilities.
- Segment networks: Separate smart devices from critical business systems to limit the impact of a potential breach.
- Implement access controls: Restrict access to smart devices based on user roles and permissions to prevent unauthorized usage.
Conclusion
In conclusion, the journey through implementing cybersecurity measures for small businesses sheds light on the critical steps needed to fortify against cyber threats. By staying informed, proactive, and vigilant, small businesses can navigate the digital landscape with confidence and resilience.
Detailed FAQs
What are the key elements to consider when planning cybersecurity measures for small businesses?
When planning cybersecurity measures for small businesses, key elements to consider include conducting a risk assessment, implementing employee training programs, securing network infrastructure, and developing an incident response plan.
How can small businesses enhance data protection using encryption methods?
Small businesses can enhance data protection by implementing encryption methods such as AES, RSA, and SSL/TLS to secure sensitive information and communications.
What are some best practices for integrating cybersecurity measures into mobile app development?
Best practices for integrating cybersecurity into mobile app development include conducting regular security audits, implementing secure coding practices, and using encryption to protect data transmission.