Mobile app security best practices take center stage in ensuring the safety and reliability of mobile applications. Delve into a world of essential knowledge as we explore the key strategies to protect your mobile apps from potential threats.
In this comprehensive guide, we will discuss the importance of mobile app security, common threats faced by mobile applications, and the best practices to secure mobile computing and software development.
Mobile App Security Best Practices
Mobile app security is crucial in today’s digital age where smartphones have become an integral part of our daily lives. With the increasing use of mobile applications for various tasks like banking, shopping, communication, and more, it is important to ensure that sensitive data and information are protected from cyber threats.
Common Security Threats Faced by Mobile Applications
Mobile applications are vulnerable to a variety of security threats that can compromise user data and privacy. Some common security threats faced by mobile applications include:
- Poorly secured data storage
- Weak server-side controls
- Insufficient encryption
- Insecure data transmission
- Unauthorized access to data
Consequences of Inadequate Mobile App Security Measures
Inadequate mobile app security measures can have serious consequences for both users and app developers. The repercussions of poor security practices include:
- Data breaches leading to loss of sensitive information
- Financial losses due to fraud or theft
- Damaged reputation and loss of user trust
- Legal liabilities and regulatory fines
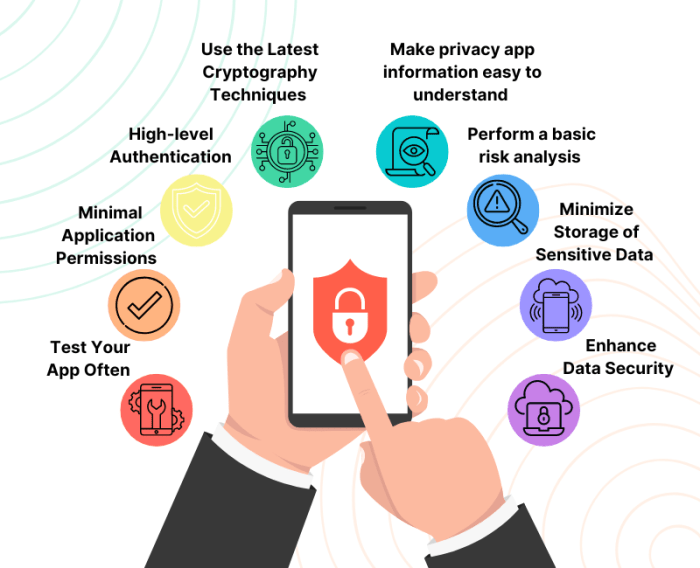
Best Practices for Secure Mobile Computing

When it comes to secure mobile computing, there are several best practices that can help protect your data and information. From securing data transmission to implementing strong authentication methods, these practices are essential for ensuring the security of mobile devices and applications.
Securing Data Transmission
Securing data transmission is crucial to protect sensitive information from unauthorized access. Here are some methods to ensure secure data transmission:
- Use encryption protocols such as SSL/TLS to encrypt data in transit.
- Implement secure communication channels to prevent data interception.
- Regularly update security protocols to address emerging threats and vulnerabilities.
Authentication Methods for Mobile Devices, Mobile app security best practices
Authentication is key to verifying the identity of users and ensuring only authorized individuals have access to mobile devices. Here are different authentication methods for mobile devices:
- Biometric authentication, such as fingerprint or facial recognition.
- Two-factor authentication combining something you know (password) with something you have (smartphone).
- Single sign-on solutions for seamless authentication across multiple applications.
Secure Coding Practices for Mobile Applications
Secure coding practices are essential to prevent vulnerabilities in mobile applications that could be exploited by attackers. Here are some examples of secure coding practices for mobile applications:
- Avoid hardcoding sensitive information like passwords or API keys in the code.
- Implement input validation to prevent injection attacks and buffer overflows.
- Regularly update libraries and dependencies to patch known security vulnerabilities.
Software Development Guidelines for Mobile App Security
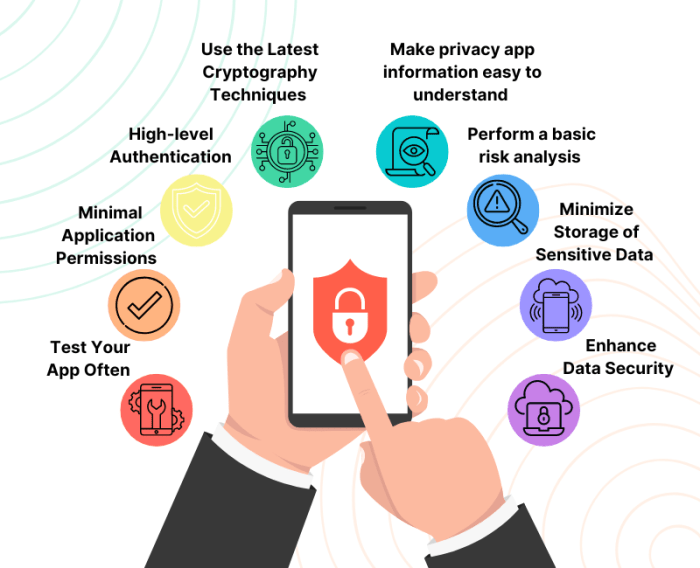
When it comes to ensuring the security of mobile apps, software development guidelines play a crucial role in protecting user data and maintaining the integrity of the application. Let’s delve into some key practices that developers should follow to enhance mobile app security.
The Role of Encryption in Ensuring Mobile App Security
Encryption is a fundamental aspect of mobile app security, as it helps protect sensitive data from unauthorized access. By encrypting data, developers can ensure that even if the information is intercepted, it remains unreadable without the proper decryption key.
- Encrypting data at rest and in transit using strong algorithms and keys.
- Implementing end-to-end encryption to secure communication between the app and servers.
- Regularly updating encryption protocols to adapt to evolving threats and vulnerabilities.
The Significance of Regular Security Updates for Mobile Apps
Regular security updates are essential to address newly discovered vulnerabilities and patch existing security flaws in mobile apps. Failing to update the app leaves it vulnerable to attacks and compromises user data.
- Monitoring security advisories and promptly applying patches released by the platform providers.
- Implementing automated update mechanisms to ensure users are running the latest secure version of the app.
- Educating users on the importance of updating their apps to protect against security threats.
The Importance of Implementing Secure APIs in Mobile App Development
Secure APIs are critical for maintaining the security of mobile apps, as they serve as the interface for communication between different software components. By implementing secure APIs, developers can prevent unauthorized access and data breaches.
- Using authentication mechanisms such as OAuth to control access to APIs and protect sensitive data.
- Implementing proper authorization checks to ensure that only authorized users can access specific functionalities.
- Regularly auditing APIs for security vulnerabilities and conducting penetration testing to identify potential risks.
Hardware Considerations for Enhanced Mobile App Security
When it comes to enhancing mobile app security, hardware plays a crucial role in providing an added layer of protection. By leveraging hardware security features, developers can ensure that sensitive data and information are safeguarded from potential threats.
Hardware-based security mechanisms offer a higher level of security compared to software-only solutions. These mechanisms are embedded in the physical components of the device, making it harder for malicious actors to compromise the security of the mobile app.
Hardware-based Security Mechanisms
- Secure Enclave: A secure enclave is a separate hardware component within the device that stores sensitive data such as passwords, encryption keys, and biometric information. This isolated environment ensures that this critical information is protected from unauthorized access.
- Trusted Platform Module (TPM): TPM is a microcontroller that provides secure storage and cryptographic functions. It helps in securing the integrity of the device by verifying the boot process and ensuring that the operating system has not been tampered with.
- Hardware-backed Keystore: Hardware-backed keystore utilizes the secure element present in the device to store cryptographic keys securely. This ensures that encryption keys are protected from software-based attacks.
Impact of Device Tampering
- Device tampering can compromise the security of the mobile app by allowing attackers to gain unauthorized access to sensitive data.
- Rooting or jailbreaking the device can bypass security controls and give attackers elevated privileges, making it easier for them to exploit vulnerabilities in the mobile app.
- Modification of the device’s firmware or operating system can introduce malware or backdoors, putting the security and privacy of the user at risk.
Ending Remarks
In conclusion, implementing robust security measures is crucial in safeguarding mobile applications against malicious attacks. By following the best practices Artikeld in this guide, developers can ensure the integrity and confidentiality of their mobile apps, providing users with a secure digital experience.
Key Questions Answered: Mobile App Security Best Practices
How can encryption enhance mobile app security?
Encryption plays a vital role in safeguarding sensitive data stored and transmitted by mobile applications. By encoding information in such a way that only authorized parties can access it, encryption helps prevent unauthorized access and data breaches.
Why are regular security updates important for mobile apps?
Regular security updates are essential to address newly discovered vulnerabilities and patch existing flaws in mobile applications. By keeping software up to date, developers can mitigate potential risks and ensure that their apps remain secure against evolving threats.
How do hardware security features contribute to mobile app security?
Hardware security features, such as secure enclaves and biometric authentication sensors, enhance the overall security of mobile devices by providing an additional layer of protection against unauthorized access and tampering. These features help secure sensitive data and strengthen the integrity of mobile apps.